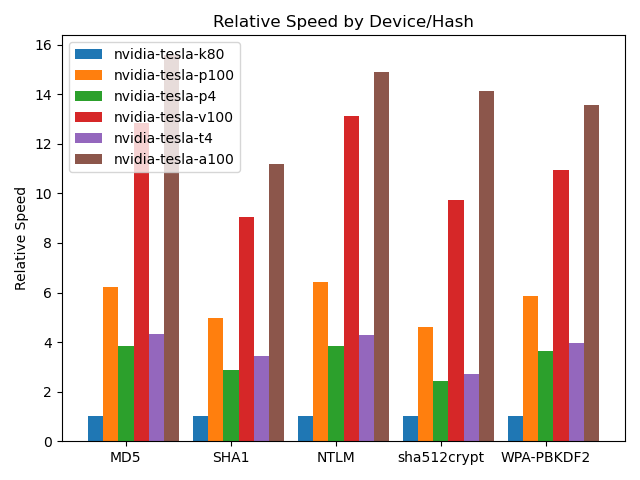
How to Crack Passwords in the Cloud with GPU Acceleration (Kali 2017) - Black Hills Information Security
How to Crack Passwords in the Cloud with GPU Acceleration (Kali 2017) - Black Hills Information Security

Minimal Memory Algorithm. The password database is divided evenly among... | Download Scientific Diagram

Applied Sciences | Free Full-Text | OMECDN: A Password-Generation Model Based on an Ordered Markov Enumerator and Critic Discriminant Network

Divided Password Database Algorithm. The password database is divided... | Download Scientific Diagram